Understanding Denial-of-Service (DoS) Attack

Introduction to Denial-of-Service (DoS) Attacks
What is a Denial-of-Service (DoS) Attack?
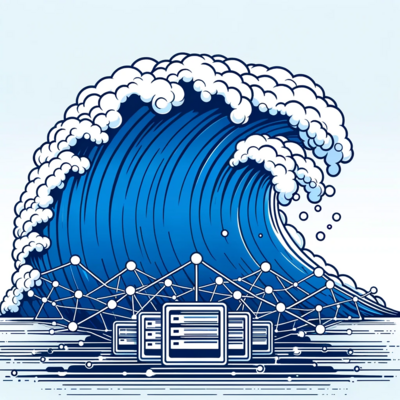
A DoS attack is a way to block a website so that no real user can access the website. This can be done by using an internet-connected device to send a huge amount of data to the target, leading to overload and unavailable for the real users.
Types and Mechanics of DoS Attacks
To exploit different aspects of the target network’s communication protocol different types of DoS attacks can be done such as TCP SYN flood attack, ICMP flood, and HTTP flood.
- TCP SYN Flood Attack: The attacker sends a large amount of successive SYN requests to the target but does not respond to the final ACK to complete the handshake. This disrupts the services.
- ICMP flood: In this type of attack ICMP requests are sent to the target mainly routers or servers This makes the server overwhelmed and eventually slows down the server’s operation and may even cause a crash of the website and unable the actual user to use the server.
- HTTP Flood: In this type of attack bandwidth consumption is less as compared to other attacks, attackers make HTTP requests to overload web servers or applications.
How DoS Attacks Work?
- Buffer Overflow Attacks: In this type of attack, the attacker exploits a bug in the program to overrun a buffer and write code in the memory spaces that can enable crashing the system or executing harmful code.
- Flood Attacks: This attack is mainly done on the network layer of the system and aims to consume bandwidth by sending a large amount of data or request to the target and making it overwhelm and unable the actual users to use the target server.
Significant Historical DoS Attacks
Over the years, the number of DoS attacks has increased rapidly, and some of the notable attacks are listed below:
- WannaCry Ransomware Attack (2017)
- Mirai Botnet (2016)
- GitHub Attack (2015 and 2018)
- Spamhaus Attack (2013)
Identifying and Responding to DoS Attacks

Signs of a DoS Attack
- Unusually Slow Network Performance: Opening of files or accessing the time is taking time longer than usual time.
- Unavailability of a Particular Website: A specific website or service is not working while others are working properly.
- Disconnection of Internet Connection: Frequent connection loss from internet services may be the cause of DoS attacks.
- Excessive Amount of Spam Emails: To overwhelm the network a lot of spam mail can be the way to do a DoS attack.
- Performance Issues on a Specific Server: A specific server is showing the issues while the other servers are working properly.
- Increased Requests Per Second: A large amount of requests are coming which is more than usual is often considered a DoS attack.
- Unusual Traffic Patterns: Traffic coming from different geographical locations can be a sign of an ongoing attack.
Immediate Steps to Mitigate DoS Attacks
- Identify the Attack: Use network monitoring tools to confirm the activities, and look at the IP addresses or traffic type, if found unusual.
- Increase Bandwidth: Though this is not a long-term solution but can be considered, temporarily increasing the bandwidth can be used to absorb the impact of a DoS attack.
- Contact Your ISP or Hosting Provider: The service provider can help in blocking malicious traffic by re-routing traffic or implementing filters.
- Implement Network Filtering or Rate Limiting: By implementing the network filter from the attacker’s IP address.
- Activate a DDoS Mitigation Service: These services can help you to absorb and filter out malicious traffic.
- Keep Software and Security Protocols Updated: Keep all your software installed with the latest security plans.
- Prepare a Response Plan: Preparing a proper plan and actions can save valuable time in responding to attacks.
Preventative Measures and Best Practices

How to Protect Against DoS Attacks
- Implement Network Security Solutions: To prevent unauthorized access and traffic use firewalls and intrusion detection systems.
- Regularly Update and Patch Systems: Always stay updated with the latest versions of your system, software, and network devices.
- Configure Network Hardware Against DoS Threats: Routers and other network hardware should be configured to limit the impact of DoS attacks.
- Deploy Redundant Network Resources: Redundancy can ensure network availability even under attack.
- Use Load Balancers: Using multiple servers to prevent the traffic on any specific server can be used to prevent any one server from getting overwhelmed.
- Employ Cloud-Based Services: Cloud services have more wider bandwidth and also help to distribute the traffic load during an attack.
- Monitor Network Traffic: Regularly monitoring the traffic can help in detecting unusual activities earlier.
- Create a Response Plan: Should have a proper planned response plan in a well-documented form to protect and respond from attack
- Educate and Train Staff: Employees should have good knowledge about the current trend of the DoS attack which can be done and should also be aware of the usual traffic of their website.
- Work with Your ISP: With the help of an Internet Service Provider, users can filter and get additional resources during the attack.
Conclusion
To prevent the attacks one must be aware of the attack and how it can be done, also should know the good tech tools, and about their network and the activities on their servers. One must have software and hardware up to date with the latest versions. Use good security systems and make your employees educated about the attacks so that detection can be easier at the early stage.